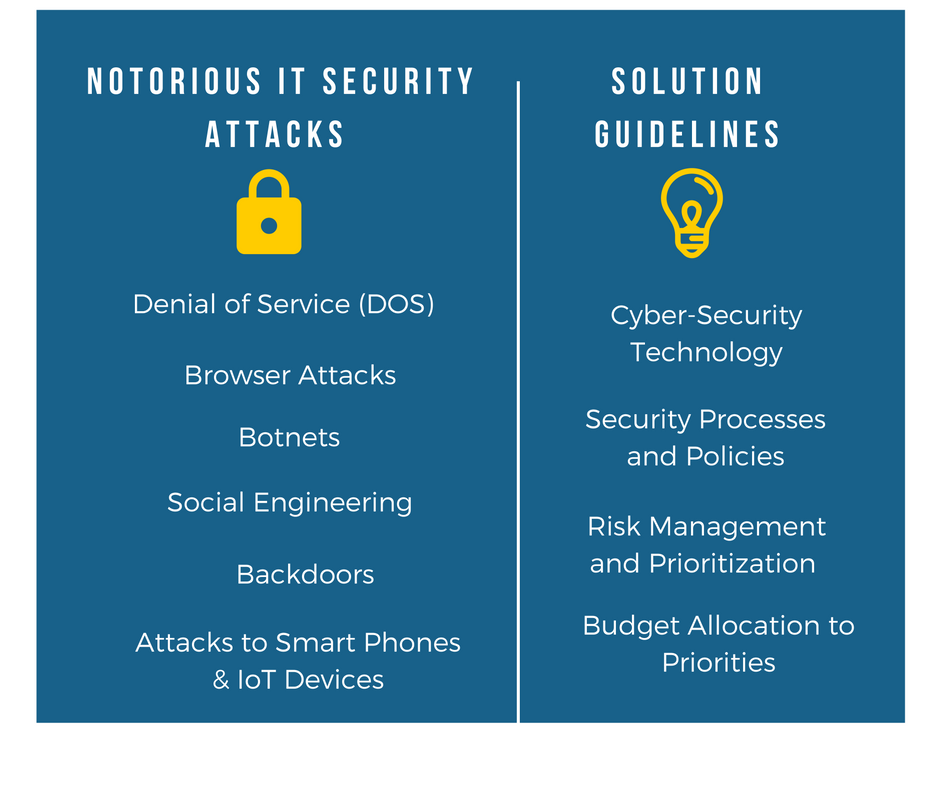
“Why do we need to invest so much in IT security?” This is a typical CFO’s quote addressed to the CIO. Security budgets are under scrutiny, as they are defensive investments rather than vehicles for aggressive growth. CIOs argue about protecting the company from disastrous risks, since they can hardly talk about return on investment and business growth. So another, more effective, way to present your argument is to highlight some of the most notorious IT Security Attacks in recent times. There are tens of types of attacks to discuss, including very prominent examples entailing the world’s biggest enterprises. Moreover, the number and type of cyber-security attacks is constantly increasing, as a result of the rising complexity of enterprise IT systems, including the rise of mobile computing and of the Internet-of-Things (IoT) paradigm. Here we pick seven (7) very recent examples for you, spanning various vulnerabilities and attack incidents.
1.Denial of Service (DOS) and Ransomware
Denial of service (DOS) attacks aim at making enterprise IT resources (such as web servers) unavailable to their users. The most common way of launching a DOS is probably overloading the system or resource with numerous malicious illegitimate requests for using the service. DOS have been around for more than fifteen years, since the notorious DOS attacks against Yahoo, FiFA, Amazon, Dell and other corporate sites back in 2000. Over time hackers have been increasing the scope and severity of these DOS incidents. In more recent years, individuals and enterprises have become victims of a specific DOS type called “Ransomware”, which locks computer systems, makes them inaccessible to their owners, and asks for ransom payments to restore them.
2. Attacking the Browser
Browsers provide our ubiquitous interface for surfing the internet. Poorly updated or inadequately patched browsers can be easily attacked causing great despair to their end-users, loss of productivity for the employees and ultimately economic loss for enterprises. There is a long list of browser-based attacks, which result in users being automatically redirected to selected web sites (e.g., to the rogue CoolWebSearch search engine) or even to display adds.
3. Backdoors
Have you ever had any internet facing networked devices (e.g., your DSL router) hacked through a point of entry (e.g., network port) compromised by hackers? That was probably a backdoor, an attack which bypasses normal security mechanisms on a computer or device in order to open back-door access from a disguised point of entry. Various telecom providers have been victims of such attacks. A recent example is Backdoor.Dripion which was created to steal information in a series of targeted attacks.
4. Botnets
Botnets are cases where groups of remote controlled hijacked computers attack IT systems. Attacks range from simple e-mail spamming to the launch of Distributed Denial of Service (DDoS) attacks. Ramnit is a famous botnet, which in 2013 allegedly affected over three million computers. It has been primarily used for financial fraud (e.g., stealing banking credentials) and was extensively spread through e-mail campaigns and phishing. Botnets can in several cases be caused by worms, which invade computers and render them a part of massive botnets. Back in 2008, the Conficker worm was exploiting the vulnerabilities of Microsoft machines and was turning them to botnet nodes which were controlled by the authors of the worm.
5. IT-related Social Engineering Attacks
Technology alone can never eliminate IT security risks. Social engineering attacks refer to the acquisition of confidential information from people (e.g., employees) through their manipulation. Such attacks reveal the need for investing in security policies and processes, as well as their enforcement. There are numerous notorious social engineering attacks, ranging from information gathering to direct stealing of passwords that enable malicious parties to access IT systems. In 2013 hackers (of the Syrian Electronic Army) managed to access the Twitter account of the Associated Press news wire service. Using this Twitter account, they reported breaking news about explosions in the White House and injury of the President. This had an immediate (yet temporary) impact causing a fall in the stock market, along with other implications. While this is impressive and rather rare, there have also been cases where administrative or IT support personnel have revealed passwords over the phone. Are you sure your assistant understands and abides by security processes?
6. Smartphone vulnerability attacks
Do you know that mobile phones can be compromised as well? The exponential rise of smartphones has given rise to cybercriminals that exploit mobile phones’ vulnerabilities in order to obtain private data through methods such as keystrokes logging and capture of screenshots. Related attacks are based on fake login screens in mobile apps (e.g., financial or banking apps), which facilitate hackers to steal and exploit private data.
7. Internet of Things Hacking
The emerging Internet-of-Things (IoT) infrastructures and devices are no exceptions to the rule that nothing and nobody is immune to hackers. IoT empowers new forms of security attacks at both the level of individual devices-things and the core infrastructure. In 2015 Chrysler recalled 1.4 million vehicles, which were vulnerable to remote hacking via the Internet. This is no science fiction: Remote hacking could enable hackers to cut the brakes, shut down the engine, or even damaging all electronics putting drivers at great risks.
Outlook
The above examples are only a few among hundreds of major IT Security attack incidents worldwide. They demonstrate that all IT systems and enterprises remain vulnerable, despite the ever increasing investments in security technologies. At the same time, they underline the importance of the human factor and of the security policies, especially in the case of social engineering attacks. Enterprises cannot afford to ignore security risks, despite possible budget concerns. The above examples and a careful risk management exercise in order to identify priorities and optimally allocate available budgets should be enough to convince your senior managers and CFO.










