If you have developed a mobile app lately chances are that it’s insecure, and vulnerable to hacks and malicious attacks.
This is one of the worrying conclusions of an IBM sponsored report “The State of Mobile Application Insecurity” released early this year.This report makes for interesting reading but some data points stick out that should be of concern to anyone who is in the business of mobile apps.
Before we dig into the report and explore the critical points mentioned let’s focus on the implications of neglecting mobile security.
A peeping Tom on your phone
According to another report published by Araxan Technologies called “State of Mobile App Security: Apps Under Attack” out of 100 top paid apps, 97% of Android apps and 87% of iOS apps have been hacked.
If you have only free apps on your mobile device you are not safe either: 80% of top free Android apps and 75% of free iOS apps have been compromised.
Vulnerabilities in these apps can let a hacker access your exact location, look through your photos, take control of your phone’s camera, read your emails and copy your contact information.
Armed with these details criminals can launch phishing attacks or social engineering hacks, ultimately gaining access to sensitive information like financial data or email passwords.
While the personal implications of data loss are bad enough the problem is exacerbated in a BYOD setting in the workplace as gaps in mobile app security can lead to real financial loss.
Mobile app security: problems and solutions
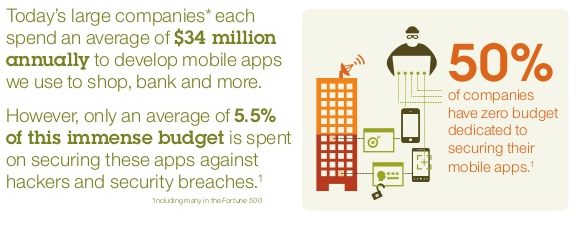
If you are involved in the business of mobile apps you would know that money is not the problem: companies spend $34million in developing apps but spend only 5.5% of this budget on security, while 50% companies have no budget for testing!
These are some problems that bedevil mobile app security according to the IBM report:
1) Speed to market compromises testing
65% of the respondents say that mobile apps are published in a fast and furious mode and the rapidly changing landscape in terms of platform fragmentation and customer demand means that apps are pushed out without developers placing enough emphasis on testing.
The solution: The “rush to release” problem is tough to solve. While there will always be a toss-up between speed and security the issue can be somewhat addressed with from proper training and code development best practices.
2) There are few controls on employee app usage
50% of respondents say that use of mobile apps by employees in the workplace have increased security risks. However 55% of respondents say that they don’t have an app usage policy in the workplace.
The lack of rules can be a problem because there is no control on what kind of apps employees can install on their devices that they also use for work.
Solution: There is a need to institute an app usage policy which outlines which apps can be installed on company owned devices, and which apps can access the corporate network in a BYOD environment.
3) Enterprises don’t test all the apps
Organizations only test 46% of the apps in use for vulnerabilities and almost a third of them (30%) contain vulnerabilities. Furthermore, 22% of respondents tested apps during deployment while 16% tested them during production.
Solution: Testing of mobile apps has to happen during production and development. When apps are tested during deployment any vulnerability that pops up would be hard to address without breaking the functionality and user experience of the app.
4) Apps are tested too infrequently
In a world where mobile operating systems undergo version changes on a quarterly basis or less many organizations test their mobile apps (internally developed or bought/outsourced) rather infrequently. Only 23% respondents say that their organizations tested outsourced/purchased apps every time the code base changes while 33% say that they don’t test either internally developed or purchased/outsourced apps.
Solution: There is a need to develop testing policies which take into account the trigger events that lead to testing of mobile apps before they are being used in the wild. Quality assurance procedures (present in 32% organizations) and security requirements (present in 36% organizations) are also necessary to streamline app security.
5) No mobile app security expertise
Only 41% of respondents say that their organizations have experts who can fix mobile app security issues. Only 30% of respondents say that their organizations have access to resources who can detect mobile app vulnerabilities while 29% of respondents have resources that can prevent the usage of malware infected mobile apps.
Solution: There is an urgent need to hire more people and allocate more resources towards catching vulnerabilities in mobile apps.
Conclusion
Like PC malware plenty of mobile malware lie hidden in devices, siphoning critical information and leaving open users and organizations to risk.
Many security aware companies are using techniques like automated scanning tools during development and after release to scan for vulnerabilities, running apps in safe environments and using encryption to secure sensitive data on the device.
What are you doing to deal with mobile app security?