Disasters are scary, and they can happen anytime to any business.
From acts of God to human malice and from natural disasters to technical troubles businesses have to be prepared for any kind of eventuality. All enterprises know this, and they invest extensively in a disaster recovery and business continuity plan. Their processes are designed and audited so that no matter what happens the show keeps going on.
This is not so for majority of small businesses.
According to data from FEMA and SBA, 40% of businesses don’t recover after a disaster and 25% fail within one year of reopening. And even more depressing is that 90% of businesses fail within two years of being hit by a disaster.
Thing is, it isn’t the lack of money or insurance that kills these businesses. It’s the lack of systems and processes.
Know your disasters
As Sun Tzu wrote in the Art of War if you know yourself and know your enemy you can win any battle.
So before you rush headlong into setting up data backups or installing fire alarms you have to audit yourself and also prioritize the potential risks.
What you will do first is build a Business Impact Analysis which identifies the services that support essential business functions.
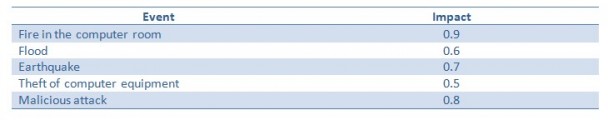
Grade the impact of events happening on a scale from 0.0 (no impact on business) to 1.0 (total shutdown of operations), and build something like this
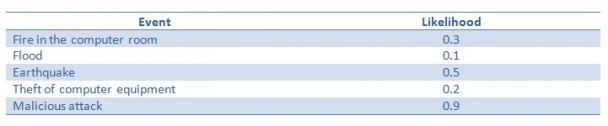
Once you know the impact of these events you can now estimate the likelihood of these events occurring using the same scale (0.0 for no likelihood, 1.0 for high likelihood) and create the following table.
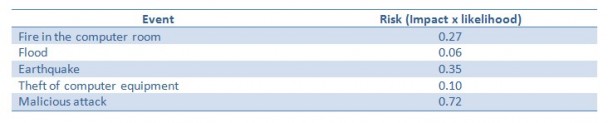
And then to get the risk that these events pose to your business multiply the impact with the likelihood to get the Risk Impact Assessment.
These numbers will be subjective and will keep changing with time. But after this exercise you will now know what to focus on- first, preventing a malicious attack, and next, taking precautions against earthquakes.
When you are conducting this exercise think not only about IT but look into every aspect of your business holistically.
Building a DR plan
Let’s assume that you want to build an effective IT recovery plan. Once you have carried out the Risk Assessment and Business impact analysis, here’s what you should do according to the National Institute of Standards and Technology:
- Identify preventive controls.
- Develop recovery strategies.
- Develop an IT contingency plan.
- Plan testing, training, and rehearsing.
- Plan maintenance.
Build separate checklists for each of these points. For example, the checklist for preventive controls should include, at the minimum the following items:
- All security software is updated.
- All versions of operating systems are updated.
- All mobile apps and other applications are running their latest versions.
- Users are sensitized against clicking on links in emails sent from unknown senders.
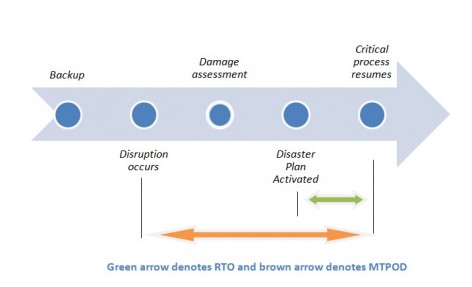
When you are building and implementing a DR plan you have to keep in mind two metrics: RTO (Recovery Time Objective) and MTPOD (Maximum Tolerable Period of Disruption). The timeline below will give you an idea of how these two metrics are calculated, and a good disaster response will aim to keep these times to the minimum.
Conclusion
Disaster recovery is a continuous process which will get more complex as your business scales and grows.
You have to secure your assets and your apps, files and the network, and actively be on the lookout for any potential security holes. This extends not only to IT but to the physical aspect of your operations as well.
Disaster recovery is a part of business continuity planning. BCPs encompass all the other processes that a business needs to implement so that business operations don’t pause even in the midst of a disaster.
To further aid your DR effort check out these links from the US Small Business Administration about how to plan for disasters.
If you haven’t yet planned for disasters start today. It’s never too late to begin, and every box crossed off your checklist takes your small business in that 10% of companies who survived and thrived two years after a disaster.